Flashback to 2013 — I picked up a Synology NAS and, honestly, it was rock solid. Fast-forward over twelve years later, and while Synology still had my respect (no issues, super stable), I felt like it was time for a change. Not because it failed me — but because I wanted something a little more focused.
Here’s the thing: Synology does a lot. It’s got apps, media servers, Docker, file syncing, you name it. But me? I used it for one job — storage. That’s it. No Docker containers. No Plex. No fancy iSCSI mounts or NFS shares. I just wanted fast, reliable storage with a 10 Gbps port — and none of the extra fluff.
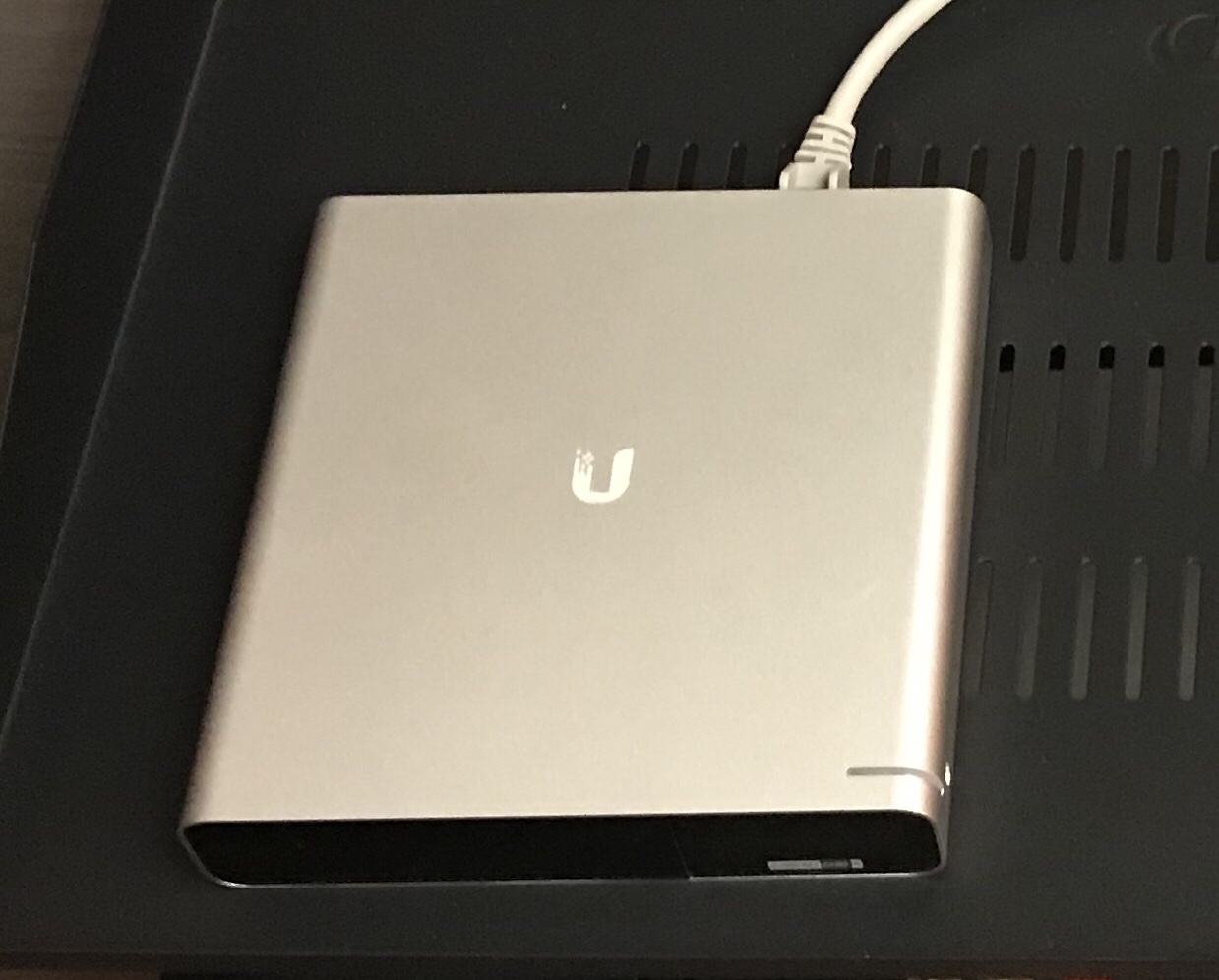
So I started looking around. That’s when I came across the Ubiquiti UNAS Pro — a slick little 2U, seven-bay NAS that’s been out for about a year now. After bingeing 40+ hours of YouTube reviews (yes, really), I thought: Let’s do this.
And wow — it nailed it.
Storage? Check
Speed? Check
Setup time? Maybe 10 minutes.
Dashboard? The classic Ubiquiti interface I already knew and loved.
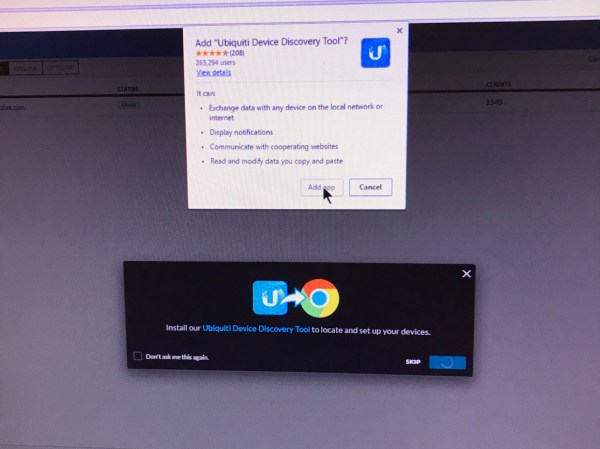
If you’re already living in the Ubiquiti ecosystem, adding the UNAS Pro is a breeze. And if not, you can still run it standalone — but trust me, life’s just easier if you fold it into a Dashboard Site. You get better control, smoother configuration, and everything in one clean view.
So, if you’re like me — and just want your storage to be storage (no extras, no distractions) — this thing is a dream. Don’t expect it to run your media empire(hmm) or spin up VMs — that’s not what it’s for. It’s built for one job, and it does that job really well.
Bottom line?
UNAS Pro is simple, fast, and focused.
And in my opinion?
….. Absolutely perfect.